People ID & Security Solutions
TRAKTERM Biometrics
bioLock
For SAP Fraud Prevention and Clear Accountability.

bioLock for SAP Security: Biometric Access and Function Control
To protect sensitive business processes and data in SAP, the security solution bioLock secures access and functions with biometric authentication.
Fingerprint, hand vein scan or other individual features therefore become a type of security key.
bioLock documents all accesses and guarantees that activities may only be performed by the person who is logged into the SAP system and authorized to perform them.
Business Challenges Running SAP
SAP SEcurity GAP
Despite SAP’s dominant market position, security is an on-going functional gap
Costly Data breaches
Data breaches becoming more prevalent, publicized and costly

Single-authentication SAP passwords are not encrypted
Single-authentication SAP passwords are not encrypted; username and passwords credentials at risk
BREACH PREVENTION
Data breaches can be difficult to prevent and take time to detect
bioLock - Securing various SAP function levels
bioLock offers far more than just simple access protection. With bioLock, even fields, functions, or values within the SAP system are specifically protected and released.
Anybody trying to access the balance sheet or review personnel data now must authenticate themselves by fingerprint to prove they are authorized. bioLock makes it impossible to obtain access to unauthorized functions using a third party user profile.

Protect your balance sheet with authentication with fingerprint
More security with biometrics
As the only biometric control software solution, bioLock controls access and function to and in the SAP system. Users are authenticated through their fingerprint, which is compared with the stored reference data. bioLock documents all access attempts and ensures that functions are actually executed by the person who is registered in the SAP system and who has the corresponding user rights.
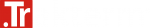
Hand vein authentication
Fujitsu PalmSecure™ is a biometric authentication solution that identifies a user with a scan of his hand vein pattern. Combined with the bioLock™ application, PalmSecure is an extremely reliable solution that prevents unauthorized, non biometrically-verified access to data.
Your Benefits
- Effective protection of sensitive data and critical functions in the SAP system
- Reduction of internal IT costs and administrative effort
- Single sign-on via fingerprint or hand vein authentication for all systems
- Use of digital signatures
- Documentation of all activities of identified users on the SAP system
- Dual control principle
- Support of biometrics and smartcard
- Minimization of theft risk and protection against manipulation
- Tamper-proof and GRC-secure documentation and control of critical function